How to Stay on Top of Cybersecurity News
The top tools and news sources you need to know if you are in cybersecurity. Don’t get caught off guard by an attack!
The top tools and news sources you need to know if you are in cybersecurity. Don’t get caught off guard by an attack!
How to audit and better secure Active Directory passwords. The latest updates to enterprise password policy and best practices. Tips on how you can stay up to date on breaches.

If you are not using these free tools to secure Active Directory, then you’re an easy target! Find the vulnerabilities lurking in your Active Directory environment before the attackers do.

How you can create fun and engaging cybersecurity tabletop exercises at your organization. Fulfill compliance requirements for tabletop exercises or security awareness training with the provided documents.

How to securely create a Windows Scheduled Task that requires high domain level privileges. Leveraging standalone Managed Service Accounts(sMSA) to automate administrative tasks.

Many Active Directory attacks’ root vulnerability is the domain’s AD Access Control Lists. This post explains what you need to know about the AD Access Control List to prevent lateral movement and escalation of privileges in the domain.

The tips you need to know for the Hack The Box Dante Pro Lab challenge. Are you ready for the challenge? My review of Hack The Box’s Dante Pro Lab.

Are you defending PowerShell abuse in your network? Find out the PowerShell best practices for preventing abuse.

How to deobfuscate malicious PowerShell using a real-world example. Learn what you need to know now before an incident occurs!

Do you have a Data Collection Incident Response Plan? Here is a method to jump-start the process.
Learn to audit for and prevent DCSync attacks in your Active Directory environment. Most other sources miss more attack paths to DCSync abuse. Find all the DCSync attack paths; if you don’t, the Attackers will.

Many Active Directory attacks’ root vulnerability is the domain’s AD Access Control Lists. This post explains what you need to know about the AD Access Control List to prevent lateral movement and escalation of privileges in the domain.
Dive into the IT professional’s nomadic journey—conquering ergonomic hurdles and fortifying digital defenses. Uncover essential tips for a seamless blend of work, travel, and security. Your IT adventure begins here!

A walk-through for the Let’s Defend DFIR Remote Code Execution challenge. A forensic investigation with Obfuscated PowerShell, reverse shells, and web shells.
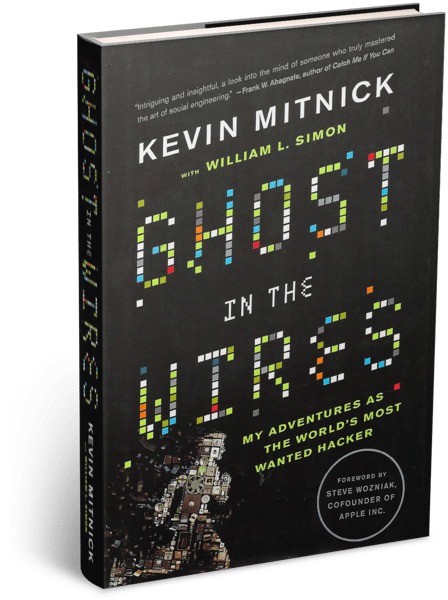
My review of Ghost in the Wires: My Adventures as the World’s Most Wanted Hacker, is Kevin Mitnick’s autobiography.
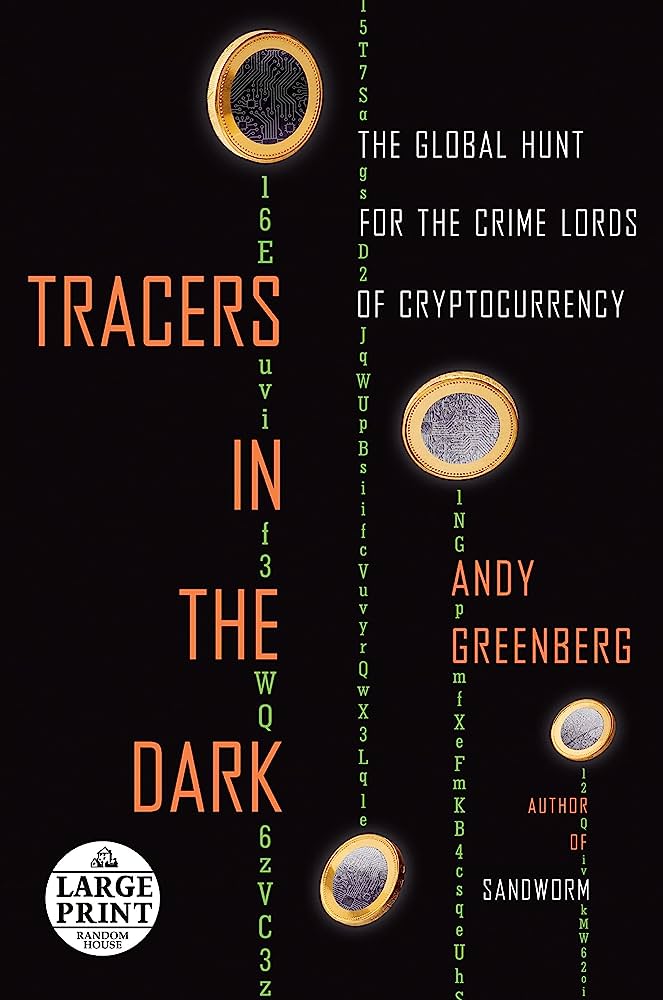
My review of “Tracers in the Dark: The Global Hunt for the Crime Lords of Cryptocurrency”. TLDR: Its a must-read.

Learn how to make your own Bash code obfuscated backdoor to hide in Linux systems.

Learn how to build obfuscated Bash backdoors with some help from ChatGPT. Can Hackers use ChatGPT to build them the Bash malware they need? Find out in this blog post.
