The cybersecurity news world moves fast! A vulnerability will go public; within 48 hours, we will see it exploited in the wild. So, as cybersecurity professionals, we always have to look for the next attack.
Staying on top of the latest vulnerabilities or tactics threat actors use is a continuous challenge. So, I want to share some of the best resources and tools I use to stay on top of the industry happenings.
Update: 8/2023
InfoSec Twitter has dramatically changed since I posted this in August of 2022. In a report by Cyentia, they estimate a 74% to 87% overall drop in Tweets with CVE discussions. CVE discussion on Twitter provided a risk impact and situational awareness of a CVE’s use by attackers. For this reason, tools like “CVE Trends” were created. However, now that Twitter is charging an excessively high fee for its API, tools like “CVE Trends” are dead.
I plan to update this post in the coming weeks.
To witness the bleeding edge of the cybersecurity world, Twitter is the place you need to be. The majority of security professionals congregate and discuss everything here. Hackers “Security Researchers” live tweet reverse engineering malware samples. Threat analysts discuss the latest tactics and attacks in real-time. If you are in cybersecurity, you need to be on Twitter.
If you want a list of good cybersecurity-related accounts to follow, check out my follow list; @CyberGladius.
CVE Trends

New CVEs go public daily, and knowing which ones to care about is a real challenge. “CVE Trends” helps take the guesswork out of knowing when to jump on patching a vulnerability. As I stated earlier, Twitter is where security professionals talk about issues. CVE Trends tracks tweets related to a CVE and exploits from researchers and security professionals on Twitter. The aggregate tweet data produces a chart of the top trending CVEs. If a CVE makes it onto this chart, you should pay attention to it.
URL: https://cvetrends.com/Feedly
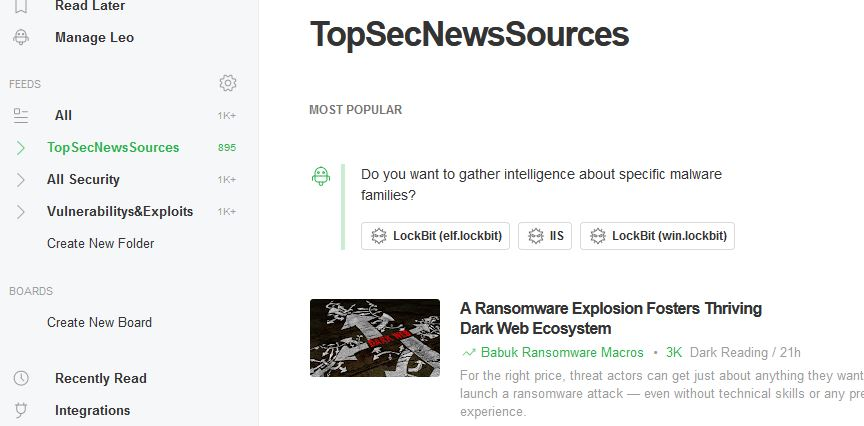
There are so many excellent cybersecurity news websites, blogs, and podcasts. Any one of those sources could contain the crucial information that you need to know. However, checking each site would be a full-time job. We can aggregate all those cybersecurity sources with an RSS feed.
The best modern RSS feed reader tool is the cloud-based tool called Feedly. Feedly can create feeds for nearly any website you give it. It also knows all the best sites related to a topic, like cybersecurity.
URL: https://feedly.comFeedly has a free and paid tier. I have a free tier account, and it works great!

SANS Newsletters
If you are looking for a concise report on cybersecurity news and don’t care to be on the bleeding edge, then SANS Newsletters are what you want. The newsletters are a by-weekly summary of top stories and threats in cybersecurity.
The SANS @Risk Report Newsletter contains a list of recent CVEs with public working exploit code. The list helps security teams prioritize patching schedules for certain CVEs. In addition, the newsletter includes a list of the most prevalent malware.
Sign up for the newsletter at the following link. The signup box is at the far-right bottom of the page.
URL: https://www.sans.org/newsletters/newsbites/
CyberWire Daily
Optimize that morning commute into the office by listening to CyberWire Daily to get the latest in cybersecurity news. The podcast covers the latest news around threat actors, malware trends, and adversarial tactics. It can get your head in the cybersecurity game in the morning and prepare you for the day.
URL: https://thecyberwire.com/podcasts/daily-podcast
Black Hills Information Security
The Black Hills Information Security team puts out a ton of excellent content. The YouTube webcast provides the best Blue Team tips I have ever received. The webcasts are a great source of learning new topics in cybersecurity.
Their podcasts are my personal favorite. The podcast feels more like hanging out with friends who are in cybersecurity and just talking about current events. It has the authentic feel that other podcasts can lack.
BHIS Blog : https://www.blackhillsinfosec.com/blog/
BHIS Webcasts : https://www.youtube.com/c/BlackHillsInformationSecurity
BHIS Podcasts : https://podcasts.apple.com/us/podcast/black-hills-information-security/id1410835265Have Any Suggestions for our List?
We couldn’t list every great source of cybersecurity news, but did we miss one you cannot live without? Let us know in the comments below!










August 8, 2022 at 2:00 PM
Good info.